 Removing programs from Windows is pretty straightforward in most cases. Merely keep on with the steps showed up as under and you will see that out how uncomplicated it can be! If you want to have an automated software utility do it and likewise clear up the left over registry keys all at one time which is beneficial by the way to remove program, a mighty uninstaller is beneficial for you sincerely.
Removing programs from Windows is pretty straightforward in most cases. Merely keep on with the steps showed up as under and you will see that out how uncomplicated it can be! If you want to have an automated software utility do it and likewise clear up the left over registry keys all at one time which is beneficial by the way to remove program, a mighty uninstaller is beneficial for you sincerely.
Apart from these there are panic button alarms, photoelectric beam detectors, and video surveillance gear that can give alerts if intruders arrive. There’s a vast array of systems to alert you to danger of many kinds. It’s good to get recommendation concerning the ones it’s possible you’ll want from those who have the required knowledge and expertise that will help you.
It is the most new approach and technology to edit.
Video convention software can be suitable with … Read the rest
 Our technology has been blessed with easier lives due to technology. We are in a position to do things faster and more efficient than most generations of the previous. Anytime you might be heading abroad on a brand new journey you need to definitely do your homework and make sure to pick the very best technology.
Our technology has been blessed with easier lives due to technology. We are in a position to do things faster and more efficient than most generations of the previous. Anytime you might be heading abroad on a brand new journey you need to definitely do your homework and make sure to pick the very best technology. Responding to this, Gawande mentioned that it is not stunning at all as many of the systems or pointers aren’t in usable type. In response to the doctor, a part of the ‘bafflement’ occurs because the folks who know how you can make such systems do not understand how the scientific encounter really operates.
Responding to this, Gawande mentioned that it is not stunning at all as many of the systems or pointers aren’t in usable type. In response to the doctor, a part of the ‘bafflement’ occurs because the folks who know how you can make such systems do not understand how the scientific encounter really operates. Before choosing the program to check with, the coed should take into consideration just a few components. The coed ought to to begin with take into accounts the credibility of the institution providing the course. The coed ought to ensure that the establishment offering the course meets and exceeds the required instructional requirements. One other issue to be considered is the general price of doing the course. The program ought to be tailored such that it meets the scholars’ wants by way of budget. It should under no circumstances hinder the coed from happening together with his/her other basic each day needs.
Before choosing the program to check with, the coed should take into consideration just a few components. The coed ought to to begin with take into accounts the credibility of the institution providing the course. The coed ought to ensure that the establishment offering the course meets and exceeds the required instructional requirements. One other issue to be considered is the general price of doing the course. The program ought to be tailored such that it meets the scholars’ wants by way of budget. It should under no circumstances hinder the coed from happening together with his/her other basic each day needs. The number of merchandise that use biometrics is increasing every single day. For private objects, there are fingerprint scanning gadgets on computers, flash drives, wallets, briefcases, and suitcases. This technology permits access only for the licensed user. This drastically impacts the extent of safety for our identification and our private information.
The number of merchandise that use biometrics is increasing every single day. For private objects, there are fingerprint scanning gadgets on computers, flash drives, wallets, briefcases, and suitcases. This technology permits access only for the licensed user. This drastically impacts the extent of safety for our identification and our private information. Windows is likely one of the most popular operating systems for a purpose – it’s extremely versatile and quick, however it is also liable to working slowly from a spread of frequent issues. There are a number of various the reason why Windows would possibly run gradual, however there’s one hidden trick that many laptop specialists & technicians use to help make their computer systems run extraordinarily fast. The good news is that this trick could be very simple to do your self, and may be done by even the largest computer novice.
Windows is likely one of the most popular operating systems for a purpose – it’s extremely versatile and quick, however it is also liable to working slowly from a spread of frequent issues. There are a number of various the reason why Windows would possibly run gradual, however there’s one hidden trick that many laptop specialists & technicians use to help make their computer systems run extraordinarily fast. The good news is that this trick could be very simple to do your self, and may be done by even the largest computer novice. If you are using a laptop, you will drain the battery life much quick whereas utilizing virtualization software. Don’t expect long battery life if engaged on the Windows facet for longer intervals of time as this may take fairly a little bit of your computer’s resources.
If you are using a laptop, you will drain the battery life much quick whereas utilizing virtualization software. Don’t expect long battery life if engaged on the Windows facet for longer intervals of time as this may take fairly a little bit of your computer’s resources. Now you know the way your computer has been your pal and helped you streamline your weight loss program. Subsequent a part of your regimen can be to plan your work out classes and intensify your exercises and exercises. You can set up comparable charts to help you monitor your workouts.
Now you know the way your computer has been your pal and helped you streamline your weight loss program. Subsequent a part of your regimen can be to plan your work out classes and intensify your exercises and exercises. You can set up comparable charts to help you monitor your workouts. If I look again to the dimly lit days that heralded my entry into business IT, approach again within the late 1980’s, I can see all the modifications that have taken place since then. I keep in mind the excitement that three.5″ disks gave me, which in flip paled compared to the shiny CD-ROM, and don’t even get me began on DVD media.
If I look again to the dimly lit days that heralded my entry into business IT, approach again within the late 1980’s, I can see all the modifications that have taken place since then. I keep in mind the excitement that three.5″ disks gave me, which in flip paled compared to the shiny CD-ROM, and don’t even get me began on DVD media.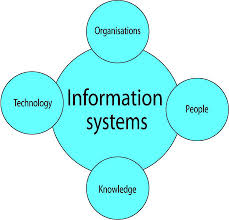 After I examined the product I found that it used a mere sixty five watts of power during its HD film display. This is by far the bottom studying I’ve encountered on a set of this high quality. There are smaller fashions that display much much less image and color high quality that consume much less. But for this magnitude of a set, this number was superb. When you have a look at the nationwide common price of electrical energy, this set only costs an individual about $1.14 to run every month.
After I examined the product I found that it used a mere sixty five watts of power during its HD film display. This is by far the bottom studying I’ve encountered on a set of this high quality. There are smaller fashions that display much much less image and color high quality that consume much less. But for this magnitude of a set, this number was superb. When you have a look at the nationwide common price of electrical energy, this set only costs an individual about $1.14 to run every month.